Discussion
Pegasystems Inc.
JP
Last activity: 2 Sep 2025 3:02 EDT
Integration tips: Call GitHub REST APIs with Installation-Access-Token
GitHub provides unique method called GitHub App for developers who want to integrate third party application with their GitHub repository. However, the authentication mechanism for GitHub App is not fully compatible with OAuth2.0 standard hence OAuth2.0 Authentication profile can not be used with GitHub connectors. This article describes the steps required to obtain an installation-access-token that enables a GitHub App to make authenticated API requests for the app's installation on a GitHub organization or individual account.
1. Register your pega application as a GitHub App in your GitHub account. (Client_ID and Private_Key will be generated for your GitHub App)
- Please follow steps described here: Registering a GitHub App
- After you create a GitHub App, you'll need to generate a private key in order to make requests to the GitHub API as the application itself. For example, you need a private key to sign a JSON Web Token (JWT) in order to request an installation access token.
2. Install your GitHub App (Installation_ID will be generated)
Please follow steps described here: Installing your own GitHub App
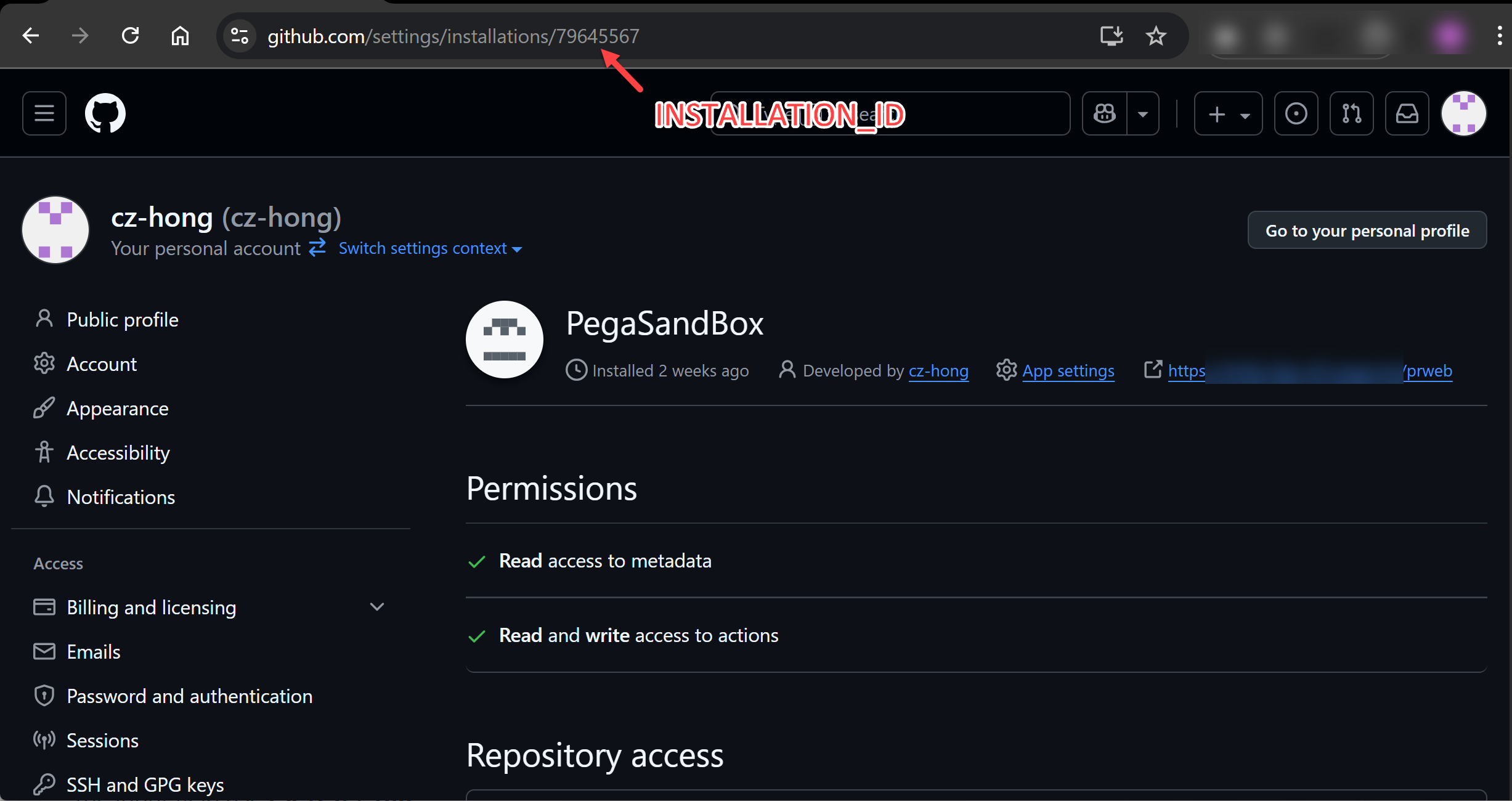
Installation_ID can be found in the URL of the GitHub App's installation settings page.
3. Create KeyStore file which contains Private_Key and it's certificate (GitHub only provides Private_Key without it's certificate, however Pega asks for a certificate when generating JWT token...)
- Create Self-Signed certificate using Private_Key for your GitHub App
openssl req -new -x509 -key {private_key.pem} -out {certificate.pem} -days {3650}
This command performs the following actions:
-new: Creates a new certificate request.
-x509: Specifies that a self-signed certificate should be generated directly from the private key, rather than a Certificate Signing Request (CSR).
-key private_key.pem: Uses the private key generated in the previous step.
-out certificate.pem: Saves the generated certificate to certificate.pem.
-days 3650: Sets the validity period of the certificate to 365 days. You can adjust this value as needed.
- Create a PKCS12 formatted KeyStore file which contains Private_Key and Self-Signed certificate
openssl pkcs12 -export -inkey {private_key.pem} -in {certificate.pem} -out {private-key.p12} -name "github-app-key"
This command performs the following actions:
pkcs12 -export: export a PKCS#12 file storing cryptographic objects like private keys and certificates.
-inkey private_key.pem: Specifies the path to the file contains private key of your GitHub App
-in certificate.pem: Specifies the path to the Self-Signed certificate for the private key
-out private-key.p12: Specifies the path to PKCS12 formatted KeyStore file
-name github-app-key: Specifies the alias name for the private key in the keystore
4. Create JWT token Profile
- Create KeyStore data instance (of class DATA-ADMIN-SECURITY-KEYSTORE)
Please follow steps described here: Configuring a keystore by uploading a file - Create JWT token profile data instance (of class DATA-ADMIN-SECURITY-TOKEN)
Please follow steps described here: Creating a generation JSON Web Token profile
Please refer Generating a JSON Web Token (JWT) for a GitHub App for values to be speficied in the token profile rule. - Preview JWT token

5. Install component "GitHub token API"
- Please download and install component "GitHub token API" to your Pega Platform.
- Enable component "GitHub token API" with your Pega Application.
6. Obtain Installation Access Token using GitHub App's Installation_ID and JWT token
provide INSTALLATION_ID and JWTProfile definition for data page: D_GitHubAccessToken.
if the data page executed successfully,
.token: contains access token which can be used as authentication bearer for api calls
.expires_at: contains timestamp when token will expire.
D_GitHubAccessToken[INSTALLATION_ID:param.INSTALLATION_ID, JWTProfile:param.JWTProfile].token
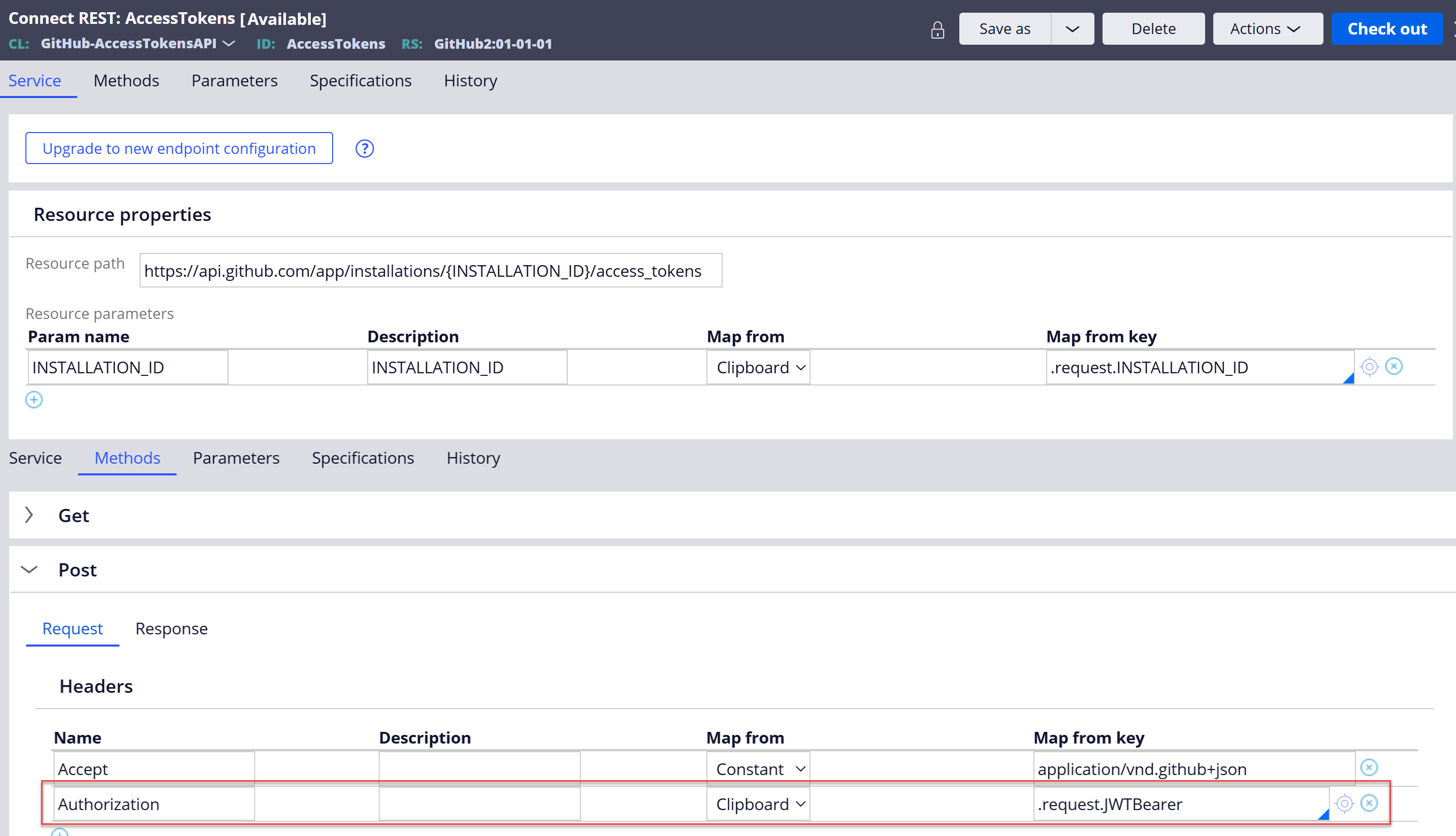
7. Create REST connector for GitHub REST API endpoint (e.x. Create an installation access token for an app)
- Please follow steps described here: Creating a REST integration by using the Create REST integration wizard
- Add parameter: "JWTProfile" to automatically created Data Page for the endpoint
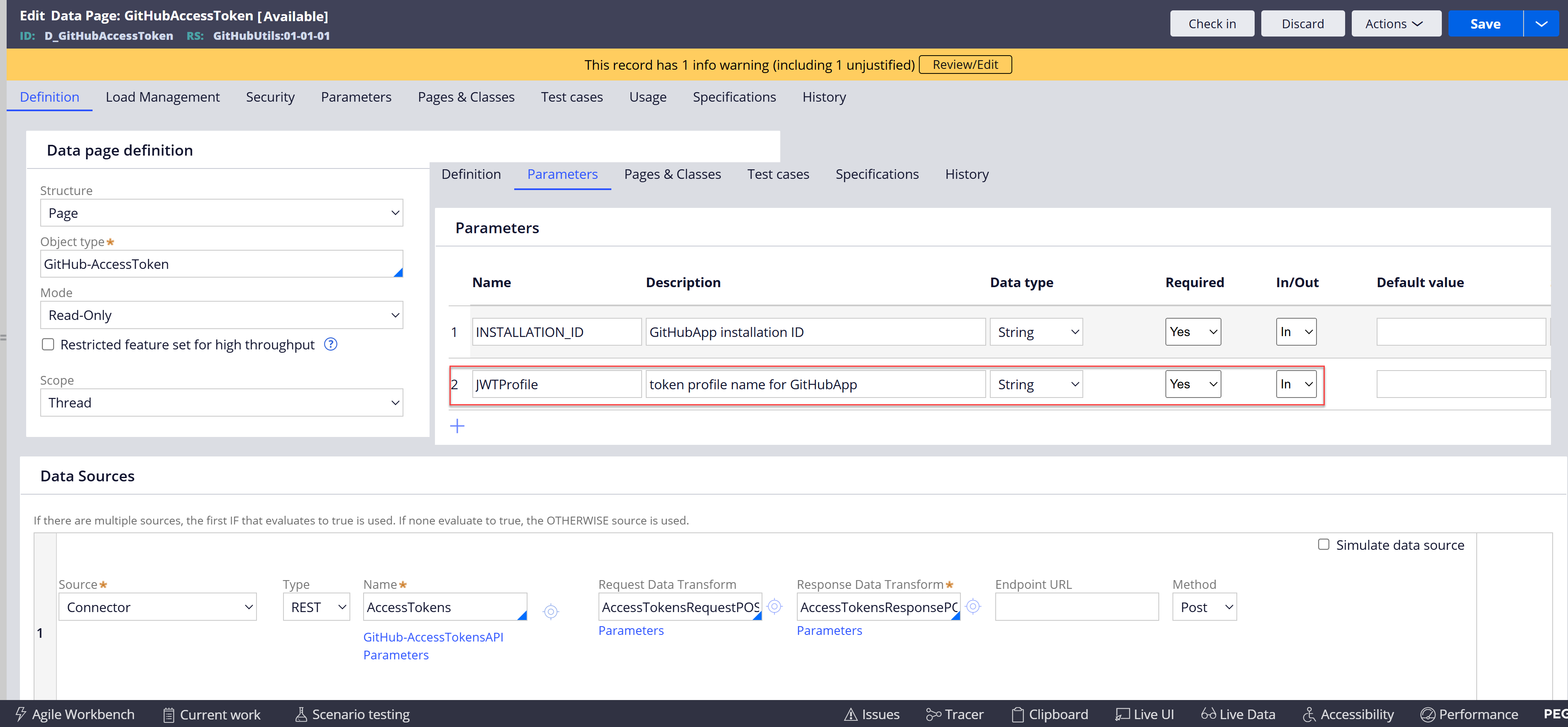
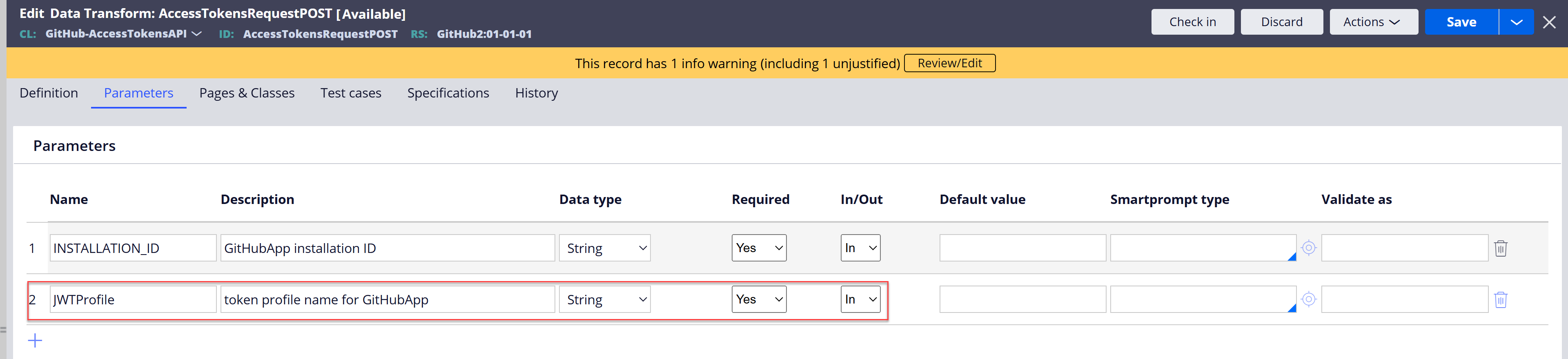
- Add parameter: "JWTProfile" to automatically created Request Data Transform for the endpoint
- Add property: "JWTBearer" to automatically created Request Data Class for the endpoint.
- Add HttpHeader: "Authorization" to the connector rule and map its value from Clipboard.
- Update Request Data Transform to set ".request.JWTBearer" value.
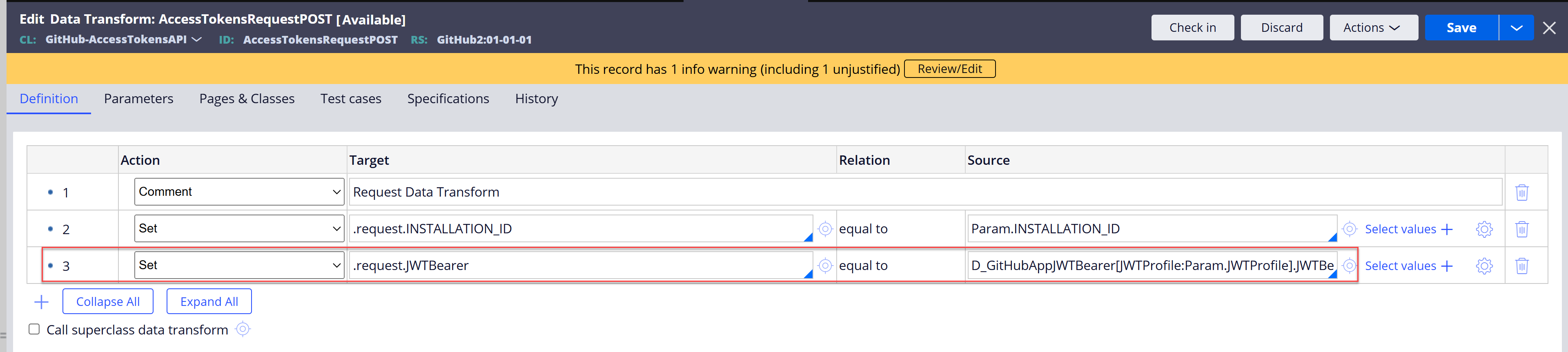
- Test connector
