Question
citi corp.pvt limited
IN
Last activity: 21 Oct 2021 8:40 EDT
AD LDAP configuration
Hi,
I am trying to connect to ad ldap but getting this error "Failed to bind to directory using bind information. Is the distinguished name similar to "cn=Admin"? javax.naming.AuthenticationException: [LDAP: error code 49 - 80090308: LdapErr: DSID-0C090447, comment: AcceptSecurityContext error, data 52e, v3839]"
Can any one help me on this.
Thanks
Shilpa
-
Share this page Facebook Twitter LinkedIn Email Copying... Copied!
Accepted Solution
Updated: 21 Oct 2021 8:38 EDT
Pegasystems Inc.
GB
Pegasystems Inc.
GB
Hi,
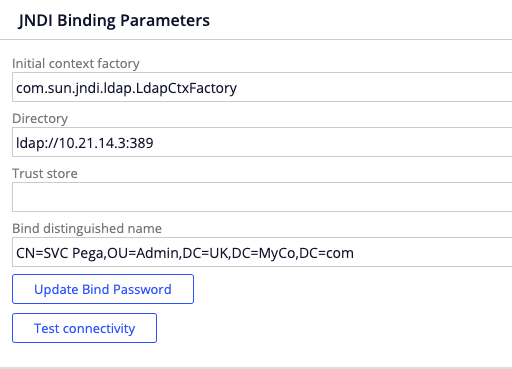
You need to review the JNDI Binding Parameters in your authentication service.
Sample if you use ldap:
Sample if you use ldaps:
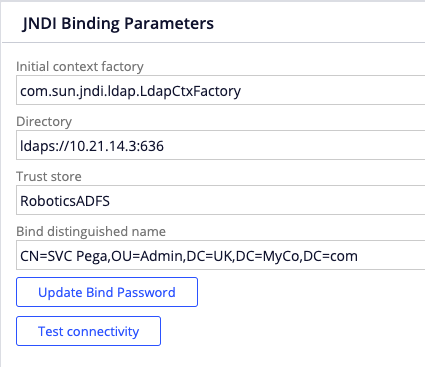
On both cases you need to provide the Bind Password for the account used. In the example the account is "SVC Pega". In your case you said it is "admin" based on the exception. You probably need to provide the full path (OU, DC(s))
citi corp.pvt limited
IN
@Angel Hermira Thank you for your reply.
Actually I have 2 doubts here can you please help me on these as well.
1. For individual users like svc pega from I am referring the bind distinguished name from that particular user(ex, svc pega) attribute properties and my connection was successful but where I am getting this error was when I am trying to refer group in BD Name means if we have user1,user2...in GRP1 so in BD name how can we refer this GRP1 so can you please help me on how to configure that bind distinguished name dynamically means how can we configure for the group of users in Bind Distinguished name (in AD LDAP )and how to set bind password for that(where we need to set that password in AD LDAP).
2. In directory(AD LDAP) now I am referring ldaps://Domain1.XXX.net:XXXX and in I have another domain which is Domain2 so how can we configure directory that will include both domains instead of creating new authentication service for Domain2.
Thanks
Shilpa
Pegasystems Inc.
GB
1.-
I'm not sure if I understand your question. This is the service account used to connect to LDAP. This is not the account used to query the values for. You specify the Binding details for the account used to connect to LDAP. This is fixed and it is typically a service account defined in LDAP to access the service. It requires query access to query any user's details (Read only)
2.-
Typically when you have multiple domains you use multiple authentication service rules. You can call these from a general authentication activity like done in the AuthenticationLDAPWebVerifyCredentials sample activity.
citi corp.pvt limited
IN
@Angel Hermira
Hi AngelHermira,
As of now we are able to connect to ad ldap when we are configuring CN(in Bind Distinguished Name ) as individual operator id instead of group. please find attached screen shot in which XXX is an individual user and able to log into pega as XXX.
So only individual user will be able to access via ldap but for other users in our organization they will not be able to access it.
we have “XYZ” group in this domain which contains list of users so can we configure pega ldap for this group instead of an individual user.
Can you please help me on this.
Thanks
Shilpa
Pegasystems Inc.
GB
The Binding information is the account used to connect to LDAP to query the details. This account is used to connect to LDAP to query details for any operator in the system using the Authentication service. This is just to establish the connection.
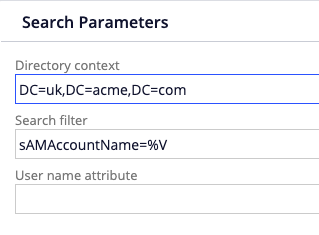
The query is defined in the Search Parameters section were you define the Directory Context for the query using DC attributes and the search filter. For this last you typically use sAMAccountName=%V were %V is dynamically replaced by when authenticating by the operator ID you are querying the details for.
Does this make sense to you?
citi corp.pvt limited
IN
@Angel Hermira
Thanks you for your response!!
I have already using the same in search params (sAMAccountName=%v). I am attaching the screen shot for the same. the thing is in CN i have given svr_pega as a user now the connection was established successfully for svr_pega but now when I am trying to login with other id in the same directory path like in the same OU then we are unable to login.
So I just want to know how the configuration should be done to allow multiple users.
Thanks
Shilpa
Accepted Solution
Updated: 21 Oct 2021 8:38 EDT
Pegasystems Inc.
GB
You are including the CN and the OUs in the Search Parameters section to define the Directory Context. You shouldn't do that. You should only include the DCs.
The Directory context is where you want to perform the search. If you include the CN and the OUs there. The search is only performed on that element.
Try to remove the CN and the OUs and to leave only the DC values. That should perform the search on that directory for any user.
Additionally, I noticed that your filter value is provided in brackets, you shouldn't need to do that nor need to provide a User name attribute.
As an example see this screenshot from a working configuration:

@shilpak1 ,
You are including the CN and the OUs in the Search Parameters section to define the Directory Context. You shouldn't do that. You should only include the DCs.
The Directory context is where you want to perform the search. If you include the CN and the OUs there. The search is only performed on that element.
Try to remove the CN and the OUs and to leave only the DC values. That should perform the search on that directory for any user.
Additionally, I noticed that your filter value is provided in brackets, you shouldn't need to do that nor need to provide a User name attribute.
As an example see this screenshot from a working configuration: